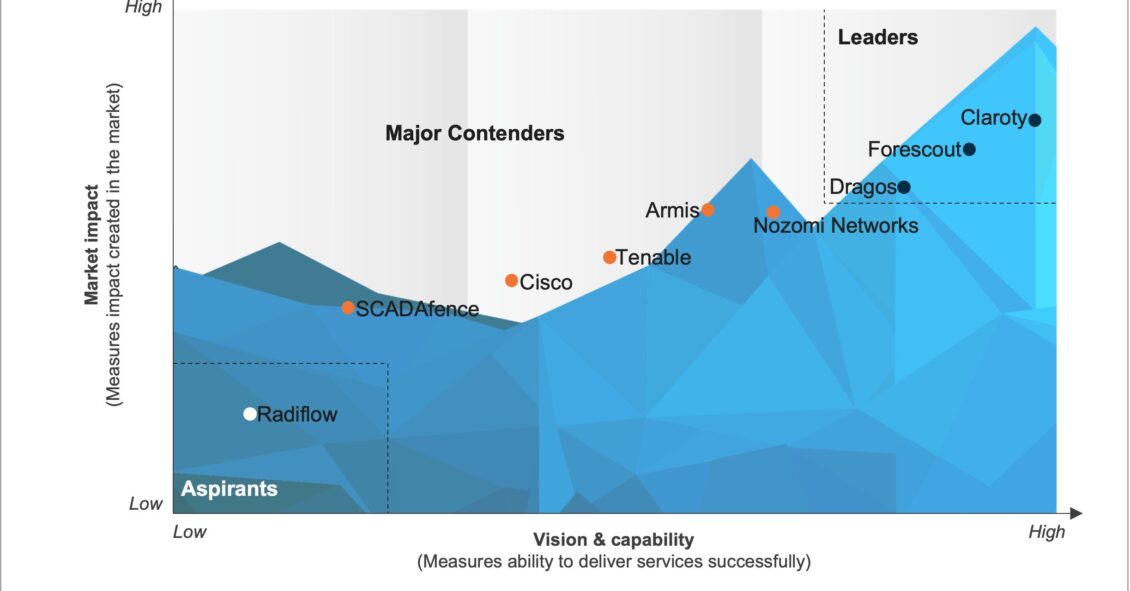
The convergence of IT and Operational Technology (OT) profoundly impacts the OT security landscape, enhancing operational efficiency while introducing vulnerabilities as traditional OT systems integrate with IT networks. Industries recognize the need to protect operational technology systems from escalating cyber threats, leading to a surge in demand for OT security. High-profile attacks on critical infrastructure drive investment in OT security solutions to ensure the integrity, availability, and resilience of essential operations.
As a result, organizations are increasingly investing in OT security measures, including network security, advanced asset visibility, threat detection, incident response plans, and risk and vulnerability management, to protect critical infrastructure and minimize cyber risks while embracing the benefits of IT/OT convergence. Technology providers are investing in next-generation themes in the OT security landscape, including AI-driven threat detection, integration of behavioral analytics, and robust cloud-based solutions. Supply chain security and collaborative information sharing are also on the rise, strengthening critical infrastructure protection and enhancing OT cybersecurity in the face of evolving threats. Technology providers are actively developing industry-specific OT security solutions for sectors such as energy, manufacturing, and healthcare. These solutions effectively address threats specific to each sector, ensure compliance with industry regulations, and maintain operational continuity. This approach offers a comprehensive and customized solution to safeguard critical infrastructure and industrial control systems. The OT security sector is actively pursuing enhanced capabilities and building a strong partnership ecosystem to combat the escalating cyber threats within OT environments.
-
Operational Technology (OT) Security Products PEAK Matrix® Assessment 2023
What is in this PEAK Matrix® Report
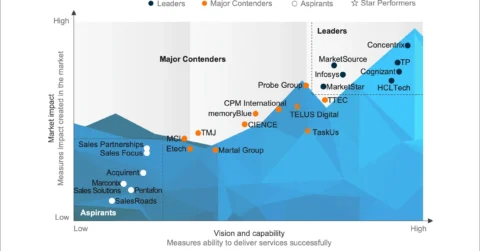
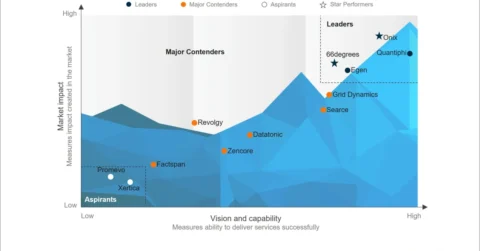
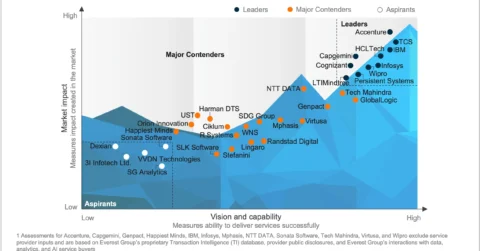
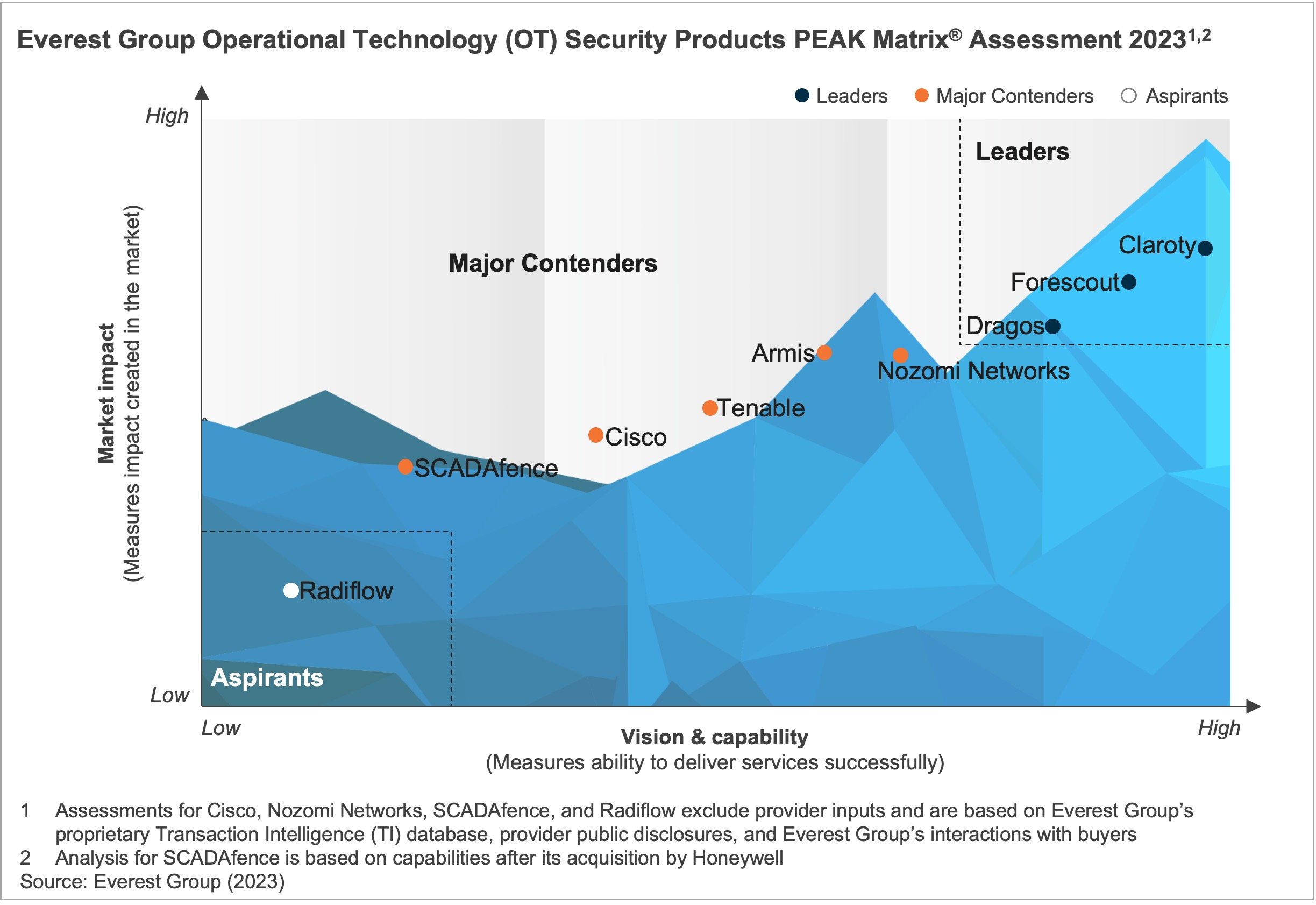
In this report, we analyze nine global OT security technology providers as featured on the Operational Technology (OT) Security Products PEAK Matrix® Assessment 2023. The research will help buyers select the right-fit provider for their needs, while providers will be able to benchmark themselves against each other.
Content:
In this report, we examine:
- OT security products PEAK Matrix® characteristics
- Enterprise sourcing considerations
- Providers’ key strengths and limitations
Scope:
- All industries and geographies
- The assessment is based on Everest Group’s annual RFI process for the calendar year 2023, interactions with leading OT security technology providers, client reference checks, and an ongoing analysis of the OT security products market
READ ON
What is the PEAK Matrix®?
The PEAK Matrix® provides an objective, data-driven assessment of service and technology providers based on their overall capability and market impact across different global services markets, classifying them into three categories: Leaders, Major Contenders, and Aspirants.