Considering the nature of regulations and the sensitivity of personal information, one would assume that IT security is a top priority in the healthcare space. However, an estimated 29 million+ patient health records have been compromised, (classified as HIPAA data breaches,) since 2009. The number of health records breached in 2013 jumped a whopping 138% over 2012. Serious security flaws have even been detected in Obamacare’s much-touted flagship health insurance exchange website, HealthCare.gov, including severe lapses spanning JSON injection, unsanitized URL redirection, user profile disclosures, cookie theft, and unprotected APIs.
An Afterthought
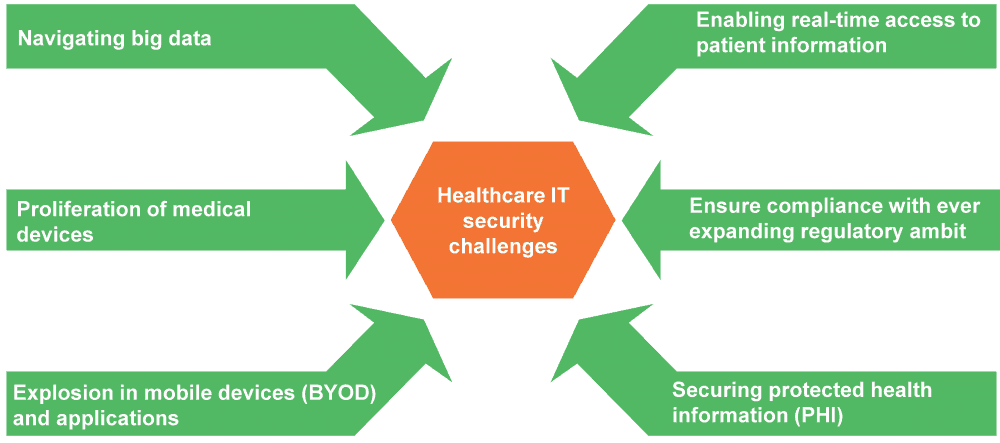
The pace at which IT is changing the healthcare landscape makes it a prime target for malicious activity. Industry headwinds such as big data, payer-provider convergence, BYOD, HIX, EHR/EMR, and the Internet of Things (IoT) are adding to the healthcare information security conundrum. Patient records have become increasingly common in the fraud marketplace. When combined with other data sources such as insurance and medical data, the problem assumes more alarming proportions.
And it’s not a case of absence of punitive measures. Under the new HIPAA Omnibus Rule (effective from September 2013), firms face fines of up to US$1.5 million in the event of a violation (“willful neglect that was not timely corrected”). Europe has enacted several data security measures. Even before the latest regulatory rulings, insurer WellPoint was fined US$1.7 million after its online application database exposed information concerning more than 600,000 patients.
Feeding the problem
Although CIOs often list security as a priority imperative, it just doesn’t translate into actual spending. This discrepancy can be attributed to a confluence of reasons. The problem originates in a lax culture regarding IT security. The majority of information security breaches are highly avoidable, and most lapses can be traced back to sloppy system administrator password practices, careless sharing of sensitive information, failure to change default login credentials, among others. Healthcare information security is still not a top execution priority for most personnel, and most security programs are hampered by lack of relevant expertise and attention. Regulatory inconsistencies compounds the issue, i.e., multiple agencies are involved (FTC, FDA, FCC, to name a few), and their often divergent mandates contribute to the travails of healthcare IT security stakeholders.
Healthcare IT security roadmap
Stakeholders – both buyers’ internal IT teams and third-party service partners –face an increasingly complex technology conundrum. Any mitigation strategy should incorporate leading practices utilized in similar initiatives:
- Conduct a thorough risk-assessment to proactively identify and secure vulnerabilities
- Establish clear level-driven permission policies (on a need-to-access basis) applicable to data, applications, and devices (keeping in mind expanding BYOD policies)
- Institute appropriate staffing practices to make sure personnel with relevant skills are given charge of security tasks
- Ensure adequate personnel training and sensitization toward information security
- Implement best-in-class encryption standards
- Collaborate with business associates (held to the same standards as HIPAA-covered entities) to establish processes and enforce standards
- Evaluate the security strategy along a security versus accessibility paradigm
- Drive synergy between the business and IT vision to avoid incoherent implementation resulting from disparate imperatives
Ultimately, any healthcare IT security policy has to encapsulate the individual needs and challenges of various stakeholders – patients, providers, payers, and third parties – to ensure equitable access and health information exchange for coordinated care. The unenviable task of securing healthcare information in the onslaught of exploding devices and touch points calls for a carefully thought-out and implemented approach. But first, healthcare IT security must make a monumental shift from being an afterthought to being a primary strategic imperative in any plan design.