Contact Center Security Best Practices for Leaders to Consider

The expanded remote work environment post-pandemic and increasingly sophisticated security threats have compelled organizations to increase their focus on protecting contact center data. Learn how to build a holistic framework of best practices for technology, the business, and agents to shape contact center security in this blog
.
Securing the landmine of customer data – from credit card numbers to health records – that reside in contact centers is a top concern for all businesses, particularly outsourced customer support. Data breaches can have serious financial, reputational, and legal consequences.
As new security threats constantly emerge and regulations change, strengthening contact center security is like aiming at a moving target. Now with the increase in remote work and more intricate ways to compromise data, this challenge has become more critical than ever. Let’s explore how it can be tackled.
Contact center security focus areas
Organizations should implement many different types of contact center security best practices related to the following three areas:
- Technology – Ensuring the organization’s devices, including bring-your-own-devices (BYODs), are up to date with the latest security systems, software patches, and firewalls. Companies also should have technology contingency plans for legacy systems that can’t be replaced
- Business – Establishing the organization has clear control and governance over its security standards and effective policies, especially in the face of ever-changing security requirements and newly emerging malware attacks and cybersecurity threats
- Agents – Providing training and monitoring of both full-time human agents and gig workers who work in the office as well as remotely
Delivery models
Contact center security protocols can vary based on the delivery model. The complexity has increased as contact centers have evolved from entirely brick-and- mortar-driven service delivery to remote service delivery with Work at Home Agents (WAHA) and BYODs, which allow agents to choose their work location and use their own devices to conduct work.
As organizations move from working at offices to remote locations, contact center leaders need to be more vigilant to keep customer data safe. While the WAHA and BYOD models bring more operational agility to the workforce, they add heightened security concerns around endpoint safety management and agent monitoring.
The below graphic illustrates how the complexity increases with the newer work models:
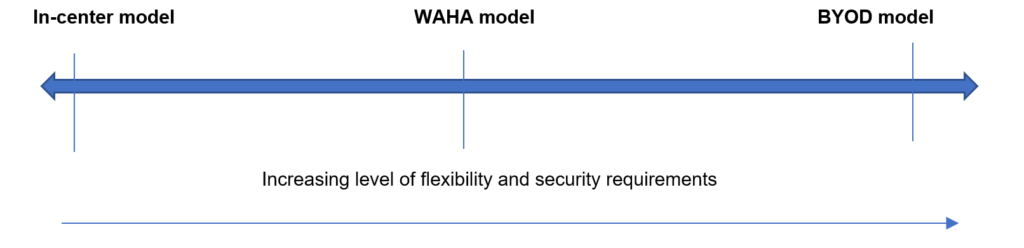
Illustration 1: Everest Group
BYOD security
Defining a BYOD security policy is critical to maintaining company security. Stakeholders from different departments are key to the policy planning process and bring important input. Leadership, human resources, finance, IT operations, and the security team should be part of a BYOD project management team and be asked to contribute to policy development.
Security patches
Failing to routinely update machines with the most updated security patches is one of the biggest cybersecurity risks. Often this failure is simply due to not having enough IT resources. Even with in-center deployments, manually patching each device is a huge drain on time and resources. This challenge is further complicated in a remote/hybrid working environment where the device is off-site.
The patching process is a key part of vulnerability management. By employing best practices that expose any conflicts with existing systems configurations on which the patch is being installed, potential downtime can be avoided. For organizations with tens of thousands of network endpoints, remote patch management offers greater control over potential vulnerabilities caused by outdated patch versions, wherever they may be located on the network. This help ensures the threat is resolved as quickly as possible.
An automated patch deployment feature gives system administrators the ability to deploy patches missing in their network computers automatically without requiring manual intervention. While automated patch rollouts seem like a no-brainer for WFH and BYOD models, they also must be considered for in-center models to reduce the resource strain on the organization’s IT department.
Identifying the most critical security issues and software updates requires strong asset and software inventory management, which can be achieved using an automated patch management tool.
After that, creating a dedicated remote patch testing environment identical to the production system (using virtualization) can help run “smoke tests” to ensure behaviors/programs do not fail before moving to production. Alternatively, an initial test can be applied to less critical systems and expanded if they perform as expected. Even with a thorough patch testing program, organizations should have a contingency and rollback plan in case something goes wrong so systems can be restored to their pre-patched state.
While most security practices are agnostic of the model in which operations are run, WFH and BYOD models require an additional layer of security considerations to stay clear of any potential cybersecurity threats.
Holistic framework
Contact center leaders must look at a holistic framework of technology, business, and agent best practices to shape their security organization. The below table encapsulates some of the strategies leaders should consider:
| In-center model | WFH Model | BYOD model | |
| Technology related |
|
|
|
| Business related |
|
|
|
| Agent related |
|
||
Illustration 2: Everest Group
As infrastructure and networks grow in size and complexity, manually managing security and compliance checklists has become increasingly difficult.
Manual operations can result in slower issue detection and remediation, resource configuration errors, and inconsistent policy application, leaving systems vulnerable to compliance issues and attacks. Automating security update rollouts can help prevent unplanned and expensive downtime and improve functionality.
This approach needs to be complemented with good governance of the security landscape, ensuring the contact center is following the latest security frameworks based on their industry. Finally, organizations need to train agents on these standards and track and monitor their devices in real-time to ensure no security gaps exist that potential cybercriminals can leverage.
To discuss contact center security solutions in more detail, please reach out to [email protected] or [email protected].
Learn more about cybersecurity, incident detection, investigation, and response in our blog, “Is Managed Detection and Response (MDR) the Holy Grail for Cybersecurity Services?”