Blog
Mythos and the illusion of enterprise security
Recent narratives around Mythos have triggered a familiar reaction, concern that enterprise environments are fundamentally broken. That conclusion misses the point. These newer cybersecurity -focused models are not introducing a new class of threats. They are exposing, at scale, what many security leaders already know but struggle to operationalize, complexity, not capability, is the real vulnerability.
Reach out to discuss this topic in depth.
What’s the buzz all about?
At its core, the Mythos is less about innovation in attack techniques and more about industrialization of known weaknesses. The real story is this, attackers no longer need sophistication when enterprises offer them pathways through fragmented architectures. The recent attention around Mythos reflects a broader shift in how modern cyber risk is being understood and demonstrated.
At their core, these initiatives showcase how attackers can chain together existing weaknesses such as misconfigurations, identity gaps, and poor integrations to move laterally across enterprise environments. What makes this significant is not the discovery of new vulnerabilities, but the ability to exploit known ones at speed and scale.
These approaches highlight a critical reality, enterprise environments today are highly interconnected across cloud, identity, endpoints, and networks, and this complexity itself has become the primary attack surface.
Is it as gloomy as it sounds?
The short answer is no, but it is uncomfortable. The longer answer is enterprises are not as exposed as these demonstrations suggest, but they are far less optimized than they believe.
While the demonstrations are compelling, they are often conducted in controlled environments with limited or inconsistent security controls in place. In real-world enterprise settings, organizations typically have layered defenses including monitoring, segmentation, and governance frameworks. This means that the success rates observed in these demonstrations are often amplified.
However, the underlying message remains important. Many organizations still struggle with inconsistent control maturity, fragmented toolsets, and gaps in identity and configuration management. The issue is less about absence of tools and more about how effectively they are implemented and integrated.
What’s the practical way forward for large organizations?
Enterprises need to stop reacting tactically and start restructuring how security is operationalized. This is not a tooling problem. It is an orchestration and prioritization problem. Large enterprises need to balance immediate risk reduction with long-term structural change.
In the near term, organizations should focus on rapidly assessing exposure by leveraging cybersecurity service providers to map attack paths, identify critical vulnerabilities, and prioritize remediation efforts. This includes patching high-risk assets and isolating lower-priority systems where necessary.
Over the longer term, the focus should shift toward continuous security. This means building capabilities for real-time observability, adaptive protection, and strong governance across identities, workloads, and networks.
Most importantly, organizations need to move away from a prevention-only mindset. Given the scale and complexity of modern environments, breaches are not a question of if, but when. The emphasis should therefore be on limiting impact, detecting threats quickly, and recovering rapidly.
What should service providers do?
This moment represents a structural opportunity for service providers to move up the value chain. Enterprises do not need more alerts. They need translated, prioritized, and actionable intelligence. Service providers have a critical role to play in operationalizing these insights for enterprises.
- First, they should build intelligent assessment layer based on existing Artificial Intelligence (AI) models (Opus 4.7 or ChatGPT 5.5) to simulate attack paths and help enterprises prioritize vulnerabilities based on business impact rather than static severity scores
- Second, they should explore deeper partnerships to gain direct access to emerging models such as ChatGPT 5.5, allowing them to translate cutting-edge research into scalable, differentiated services
- Third, they should co-innovate with ecosystem partners such as Palo Alto Networks, Zscaler, and CrowdStrike to deliver ready-to-deploy solutions that combine assessment, remediation, and continuous monitoring
At a strategic level, service providers also need to step beyond technical execution and take on the role of enterprise orchestrators for AI-led security transformation. This means bringing together the Chief Information Officer (CIO), Chief Information Security Officer (CISO), Chief Financial Officer (CFO), Chief Executive Officer (CEO), and business stakeholders to align on a unified AI strategy, with Key Performance Indicators (KPIs) tied to joint outcomes such as risk reduction, operational efficiency, and business resilience. By anchoring conversations in enterprise value rather than siloed security metrics, providers can not only drive stronger adoption but also unlock significantly larger, cross-functional budgets beyond the CISO.
Ultimately, the winners will be providers that can move quickly from insight to execution and package these capabilities into outcome-driven services.
Why MVC is the most practical path to resilience
The industry has spent years optimizing for prevention. Mythos reinforces why that model is insufficient. Resilience, not prevention, is the new benchmark. MVC is how that becomes actionable. The concept of the Most Viable Company (MVC) offers a practical way to embed resilience into the enterprise operating model.
Instead of attempting to secure everything equally, MVC focuses on identifying the minimum set of systems and processes required to sustain business operations during a cyber incident. For a global enterprise, this typically includes core manufacturing and operational technology systems, distribution and logistics platforms, revenue-critical commercial systems, finance and regulatory functions, and the identity backbone that enables secure access.
These components should be ring-fenced, continuously monitored, and designed for rapid recovery. By doing so, organizations ensure that even in the event of a breach, they can continue operating at a minimum viable level.

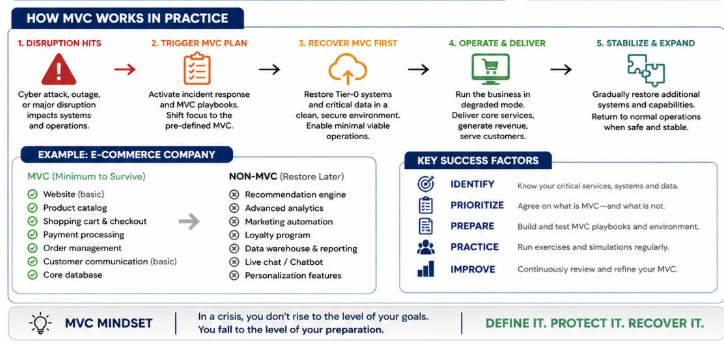
MVC shifts the conversation from infrastructure protection to business continuity under attack scenarios, making resilience a measurable and actionable objective.
Final thoughts
The takeaway is not that enterprises are insecure. It is that they are misaligned in how they define and measure security. Mythos does not introduce entirely new threats; instead, it exposes how existing gaps in security implementation and integration can be exploited more effectively.
The path forward is not to chase a hack-proof state, but to build resilience into the core of the enterprise. Organizations that succeed will be those that prioritize critical assets, integrate their security controls, leverage ecosystem partnerships, and design their operations to withstand and recover from attacks.
In an increasingly complex threat landscape, resilience is no longer optional. It is the defining capability of a secure enterprise.
If you enjoyed this blog, check out, Cybersecurity services outlook for 2026 – from evolution to reinvention – Everest Group Research Portal, which delves deeper into another topic relating to cybersecurity.
If you’d like to continue this discussion, please contact Arjun Chauhan ([email protected]) and Kumar Avijit ([email protected])